CRS Report on Vaccination Authorities
Recovery Diva
JANUARY 13, 2022
From the CRS, this 37 page report: State and Federal Authority to Mandate. COVID-19 Vaccination.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
 Authorization Related Topics
Authorization Related Topics 
Recovery Diva
JANUARY 13, 2022
From the CRS, this 37 page report: State and Federal Authority to Mandate. COVID-19 Vaccination.

Citrix
OCTOBER 5, 2022
Authentication and authorization are essential processes of identity and access management. While the terms are often used interchangeably, authentication and authorization fill different functions. The Main Differences first appeared on Citrix Blogs.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Acronis
OCTOBER 3, 2023
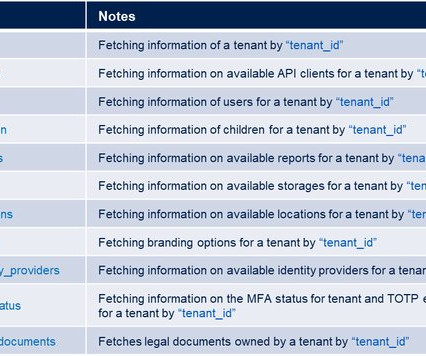
In this section, we put the spotlight on Authorization and Tenants Management, empowering you to master these crucial aspects of integration development. Whether you're a seasoned developer or new to the field, we offer training to enhance your ability to create valuable and marketable integrations.

Security Industry Association
OCTOBER 21, 2021
would require the Federal Communications Commission (FCC) to adopt rules prohibiting “equipment authorization” for certain Chinese telecommunications and video surveillance equipment. 19, the FCC had published a proposed rule that would prohibit new authorizations for equipment considered part of the FCC’s “Covered List.”

The Rand Blog
NOVEMBER 7, 2022
Congress has authorized the creation of an institution dedicated to the study and research of irregular warfare. Department of Defense may be facing a once-in-a-generation opportunity to fix a critical gap in its national security arsenal. Unfortunately, initial indications are that this opportunity might not be realized.

Behavior Group
JULY 31, 2020
The post UK authorities and allies expose Russian cyber attacks on Coronavirus vaccine development appeared first on Behaviour Portugal. The National Cyber Security Centre (NCSC) has published an advisory detailing the activities of the threat group known as APT29, which has exploited organisations globally.

DRI Drive
APRIL 15, 2024
Janko is many things – MBCP, member of the DRI Board of Directors, longtime director of global business continuity for The Goodyear Tire & Rubber Company, and now a published author.

Recovery Diva
MARCH 8, 2024
One of the authors is a former FEMA Administrator. From HSToday: Slaying the Recovery Beast: Part 1 – The Need for Program Management in Disaster Recovery. This is a useful article on the essentials of the recovery process. When the 2nd part is issued, the Diva will revise this posting.

Crisis Response Journal
OCTOBER 9, 2016
Reita Waara describes how the inclusion of large numbers of volunteers in a large oil spill exercise in the Finnish city of Kemi is so important to future emergency responses of this type. By Reita Waara

Crisis Response Journal
JANUARY 18, 2022
January 2022: Owing to the relaxation of quarantine measures, influenza – which almost disappeared last year – is returning, according to international and EU medical authorities, writes Lina Kolesnikova

National Fire Protection Association
JUNE 6, 2022
Above photo courtesy of Stephanie Schorow The Great Boston Fire of 1872 exemplified the 19th-century conflagrations that were blazing across the United States at that time. The massive fire, which came just nearly a year after the Great Chicago Fire, burned for two days in November.

Crisis Response Journal
MAY 25, 2016
In a digital age when people have many information sources, during a crisis they will not always seek guidance from the government or other official channels.

Security Industry Association
JUNE 5, 2023
Bill Edwards and Cory Peterson discuss how SIA and our members are working to advance UAS-specific authorities and regulations within the United States Code. 32 – which governs criminal acts involving aircraft, including the act of downing a drone – is a necessary step to the delegation of authorities in this operating environment.

Recovery Diva
JUNE 21, 2023
Author is Prof. From HSNW: Why Insurance Companies Are Pulling Out of California and Florida, and How to Fix Some of the Underlying Problems. Melanie Gall of ASU.
The Failover Plan Podcast
JULY 6, 2020
Episode Summary: Shane interviews business continuity industry disruptors- Dr. David Lindstedt and Mark Armour- authors of "Adaptive Business Continuity: A New Approach" and creators of the Adaptive Business Continuity movement which started in 2015. Guest Bios: Dr. David Lindstedt is a speaker, author, and champion for business continuity.

Recovery Diva
APRIL 12, 2023
This way the reader is given a roadmap to pick and choose from, if they wish so, the case studies written by various authors whose chapters span a wide variety of hazards as well as geographical and sociological settings all of which delve into a chosen aspect of disaster recovery towards building resiliency.

Recovery Diva
APRIL 1, 2023
Come Hell or High Fever Readying the World’s Megacities for Disaster Authored by: Russell W. The book is currently available as a free download. It is 498 pages and comes from the Australian National Press.

Recovery Diva
AUGUST 23, 2023
Parks, PhD, assistant professor of Environmental Health Sciences at Columbia Public Health, and first author. “In our study, excess death counts after tropical cyclones were higher more recently and for the most socially vulnerable,” said Robbie M.

The Failover Plan Podcast
JULY 13, 2020
Episode Summary: Shane continues the discussion with business continuity industry disruptors- Dr. David Lindstedt and Mark Armour- authors of "Adaptive Business Continuity: A New Approach" and creators of the Adaptive Business Continuity movement which started in 2015. 18:16min- Characteristics of those that shift to ABC today. Website. .

Recovery Diva
MARCH 15, 2023
The authors conclusion: “The lesson for my new neighbors in the United States: corruption and the erosion of democracy aren’t simply injustices, they’re deadly.” From the San Francisco Chronicle: What’s the best way to survive an earthquake? Protect your democracy.

Recovery Diva
OCTOBER 2, 2023
Federal authorities are working with wary locals to negotiate significant logistical hurdles not found in the aftermath of blazes on the mainland United States, and they are attempting to navigate the delicate dynamics of disaster cleanup in a place as historically and culturally important as the ruined town of Lahaina.

Security Industry Association
SEPTEMBER 26, 2023
Authority to Protect in Jeopardy That’s why in 2018 Congress granted federal agencies like the U.S. Last year these “authorities” were extended through congressional appropriations for fiscal year 2023, which means they expire Sept. Extension (in the latest administration proposal) of federal agency authorities to the U.S.
Security Industry Association
JANUARY 17, 2024
For more than a decade, the association has published SIA Technology Insights , which features analyses of security trends and technologies written by SIA members, and we are now seeking authors for the spring 2024 edition. We’re looking for original, vendor-neutral articles that are 750-2,500 words in length.

Bernstein Crisis Management
MAY 19, 2023
Communication and coordination: Ensuring clear and timely communication with all relevant stakeholders, including employees, customers, suppliers, authorities, and the media. Assessment and decision-making: Gathering and analyzing information to assess the situation and make informed decisions on the appropriate course of action.

Recovery Diva
JULY 18, 2022
The 17 contributing authors in the text make up extensive experience and richness in each of the chapters stemming from how disaster risk is created to call disaster risk relates to gendered vulnerability. On the topic of gender, the editors did a phenomenal job ensuring a diverse perspective of genders from the contributing authors.

Recovery Diva
MAY 12, 2022
Review by Donald Watson, co-author with Michele Adams of Design for Flooding: Resilience to Climate Change (Wiley 2011). More than twenty authors are represented in this timely book, edited by Alessandra Jerolleman and William L. He has since served in over thirty nations worldwide as consultant for United Nations, U.S.

Recovery Diva
OCTOBER 29, 2022
Another article on actions by the NY Port Authority. When Hurricane Sandy deluged New York City, leaders promised bold action. Ten years later, it’s fair to ask: What, exactly, has been done?

DisasterDoc
JUNE 7, 2021
A special guest blog from emergency preparedness and disaster survival author, Virginia Nicols. Make sure it doesn’t happen this way in your community. On October 26, 2020, over a period of. The post Near-Evacuation Reveals Dangerous Gaps in Communications for Senior Community appeared first on DisasterDoc.

The Rand Blog
MARCH 20, 2023
Congress authorized the U.S. early-stage hardware startups are seriously disadvantaged by a persistent lack of financing. Department of Defense to spend $75 million to invest in dual-use hardware startups.

Recovery Diva
JUNE 4, 2022
Author is Peter Gaynor, former FEMA Director.) Future FEMA: Reimagining Crisis Response. Congress had realized that the nation had multiple and disjointed ways it responded to a variety of major crises.

The Failover Plan Podcast
OCTOBER 12, 2020
His writing led to becoming a self published author of "BlueyedBC – Business Continuity for Junior Professionals" and most recently, becoming elected as a Director to the Business Continuity Institute’s Global Board. And we’re going to talk with him about how he developed a personal brand within our field.

Recovery Diva
MARCH 4, 2022
The authors of the report compiled methods to protect against wildfires’ two main weapons of choice: flames and airborne pieces of burning debris. NIST Offers First-of-a-Kind Guidance for Holistic Home and Community Wildfire Protection.

Pure Storage
AUGUST 3, 2023
How to Implement Threat Modeling in Your DevSecOps Process by Pure Storage Blog This blog on threat modeling was co-authored by Dr. Ratinder Paul Singh Ahuja, CTO for Security and Networking, and Rajan Yadav , Director of Engineering, CNBU (Portworx), Pure Storage. Dr. Ahuja is a renowned name in the field of security and networking.

The Failover Plan Podcast
NOVEMBER 16, 2020
Guest Bios: Dr. David Lindstedt is a speaker, author, and champion for business continuity. Along with Mark Armour he founded AdaptiveBCP.org and authored Adaptive Business Continuity: A New Approach. He is the founder of Adaptive BC Solutions (AdaptiveBCS.com) and creator of three BC software systems.

Recovery Diva
MAY 7, 2022
Author : JC Gaillard, Professor of Geography, University of Auckland, New Zealand. The author posits that the attempt to reduce disaster losses by bridging the “nature/hazard versus culture/vulnerability binary” by the Western governments in the lesser developed parts of the world has only been partially effective.

Recovery Diva
OCTOBER 13, 2021
The book has sixteen (16) chapters of which the first four were written by the editors, and the remaining twelve (12) each written by different authors. The framework introduced by the editors is applied to all the case studies covered by varying authors in the rest of the chapters. The case studies cover both the U.S.

PagerDuty
OCTOBER 26, 2023
The app will then only be authorized to access objects that the logged-in user can access, that have been included in the scopes for the app. Using a Sample App to Fetch a New User Token Once you have your app registered and have received the authorization json file, you can use the client_id and client_secret to request a token.

Security Industry Association
NOVEMBER 29, 2022
FCC prohibits new device authorizations for Chinese telecommunications and video surveillance products on the FCC's Covered List. As required by the Act, the Order prohibits new device authorizations for covered Chinese telecommunications and video surveillance products on the FCC’s Covered List.

Crisis Response Journal
AUGUST 11, 2021
August 2021: Chris Berry from Inistys explains how CCTV and the software its systems use can play a pivotal role in getting responses right and in improving overall communication between responders and authorities

Pure Storage
APRIL 17, 2024
If a ransomware event happens, payer organizations can’t process authorizations, check eligibility for benefits, and often cannot connect with their providers or members. SafeMode provides an immutable copy of data that cannot be deleted unless the authorized personnel at a customer site call Pure directly.

The Rand Blog
OCTOBER 20, 2022
Military and homeland security authorities may need to anticipate the potential use of USVs by adversaries or terrorists. The initial explosion that damaged the Kerch Strait Bridge may have come from an uncrewed surface vehicle (USV). If it was indeed caused by a USV, it could be a portent of future warfare.
Solutions Review
OCTOBER 5, 2021
Author: Mike Faucher. Author: Acronis. Author: Joeteck. Author: Acronis. Author: Scuappy’s Videos. Author: Acronis. Author: Acronis. You May Also Like. The Best Veeam Tutorials on YouTube to Watch Right Now … September 14, 2021 Best Practices. The Best Acronis Tutorials on YouTube.

The Rand Blog
JANUARY 24, 2022
Shifting those perceptions will require not just defense authorizations, but also repairing the social fabric here at home. If American deterrence fails, it may not be because adversaries doubt U.S. military capabilities so much as they doubt American willpower.

Crisis Response Journal
JANUARY 31, 2021
A new book on drone technologies, co-authored by CRJ’s Advisory Panel member Andrew Staniforth and Garik Markarian, has been published. By Andrew Staniforth and Garik Markarian
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content