Who’s the Boss? Successful Risk Mitigation Requires Centralized Leadership
MHA Consulting
FEBRUARY 23, 2023
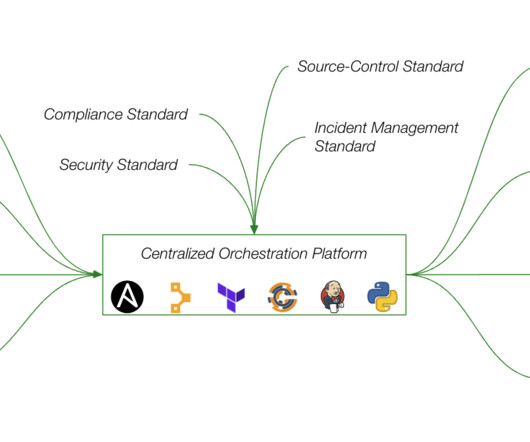
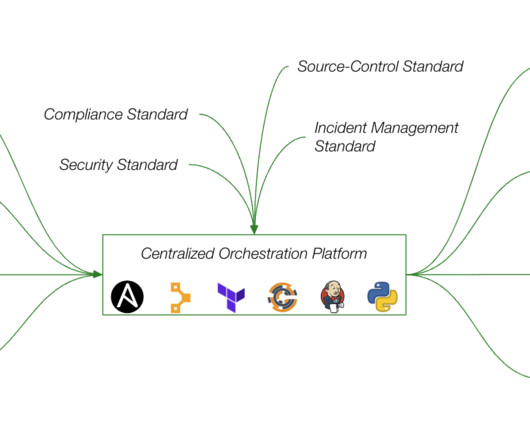
Many companies spend millions of dollars implementing risk mitigation controls but are kept from getting their money’s worth by a disconnected, piecemeal approach. Successful risk mitigation requires that a central authority supervise controls following a coherent strategy. Related on MHA Consulting: Global Turmoil Making You Ill?











































Let's personalize your content