How to Get Strong: Unlocking the Power of Vulnerability Management
MHA Consulting
JUNE 15, 2023
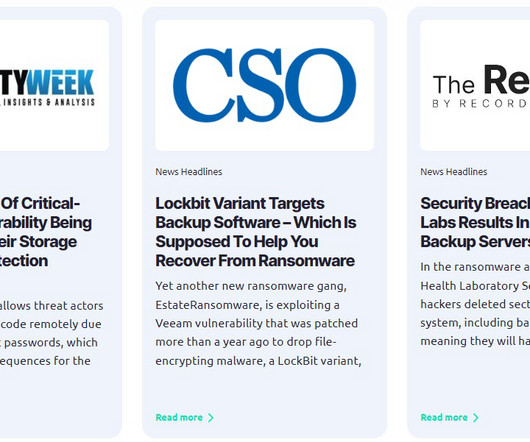
Vulnerability management is the practice of identifying and mitigating the weaknesses in an organization’s people, processes, and technology. Then we work with the client on devising a plan to mitigate those weaknesses—and do all we can to get them to follow through on the plan (otherwise, what’s the point?).














































Let's personalize your content