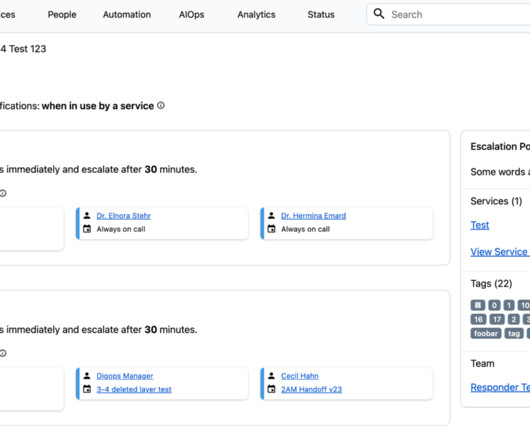
WHOIS DCV Deprecates July 15: 40% Of Firms May Face SSL Outages
Continuity Insights
JULY 14, 2025
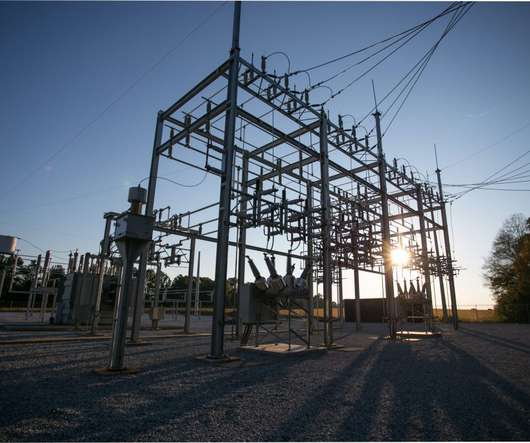
(Photo: Adobe Stock / Mer_Studio) A s many as 40% of enterprises are at risk of unexpected service outages caused by out-of-date secure sockets layer (SSL) certificates, according to new research from CSC. For years, WHOIS-based email was seen as the easiest, non-technical DCV method.














































Let's personalize your content