More online emergency management training resources
Crisis Response Journal
SEPTEMBER 27, 2018
This month Rob Fagan’s blog about free emergency management training and education focuses on a very timely and useful source: the Safe + Ready Institute.

Crisis Response Journal
SEPTEMBER 27, 2018
This month Rob Fagan’s blog about free emergency management training and education focuses on a very timely and useful source: the Safe + Ready Institute.
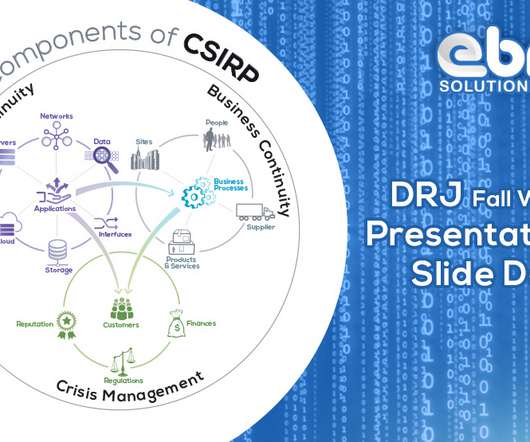
eBRP
SEPTEMBER 26, 2018
The immediate reaction to a cyber-security incident is the FUD factor (Fear, Uncertainty and Doubt); more like ‘chickens running around with their head cut off’. An agile response requires tested and documented Incident Response Plans – including Crisis Management, Business Continuity and IT Disaster Recovery Plans. Automating the workflow facilitates seamless collaboration and the ability to Monitor, Measure & Manage the activities that are critical to effective Cyber Security Incident Resp
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Alert Media
SEPTEMBER 24, 2018
The post Duty of Care: The Three Types of Employers appeared first on AlertMedia.

Behavior Group
SEPTEMBER 24, 2018
Information security threats are intensifying every day. Organizations risk becoming disoriented and losing their way in a maze of uncertainty, as they grapple with complex technology, data proliferation, increased regulation and a debilitating skills shortage. Solid Security Structure, information security threats The year 2020 will dawn on a hyper-connected world where the pace and scale… Continue reading.

Advertisement
Safeguard your IT infrastructure with our essential guide to IT Disaster Recovery (IT/DR). Learn how IT/DR supports your Business Continuity Plan (BCP) to ensure resilience in the face of inevitable disruptions. Inside the guide: BCP vs. IT/DR: Understand their roles and how they work together Key IT/DR components: Runbooks, contact lists, testing Compliance: Align with industry regulations Integration tips: Streamline planning and response Why download?

Marketpoint Recall
SEPTEMBER 21, 2018
I am so over GDPR. GDPR came into force on May 25 and it is having a profound effect on the event and corporate entertainment industry. Dreamforce is a huge user conference but also a massive exhibitor event. And as a large percentage of the attendees are from the EU, every partner exhibiting in the Expo and running parties should be concerned about GDPR.
Continuity Professional Pulse brings together the best content for business continuity professionals from the widest variety of industry thought leaders.

Crisis Response Journal
SEPTEMBER 23, 2018
Forty five years after the hostage taking that gave birth to the concept of Stockholm syndrome, Lina Kolesnikova says that emergency services workers need to be aware of the paradoxical phenomena whereby abused people develop emotional dependency on their By Lina Kolesnikova

eBRP
SEPTEMBER 9, 2018
Definition: Technology modeling is a point-in-time snapshot of an Enterprise’s IT Services – including its dependencies on infrastructure – and interfaces to other services and Business Processes which depend on them. This organizational Technology Model provides executives the critical decision support they need to understand the impacts of a service disruption.

Alert Media
SEPTEMBER 12, 2018
The post 8 Driving Safety Tips for Employees appeared first on AlertMedia.

Behavior Group
SEPTEMBER 18, 2018
Email is the single most effective and commonplace way of reaching someone in the business world today. Even as other methods of digital communication have come and gone over its 40-year history, email remains the backbone of business communications with 3.7 billion users worldwide collectively sending 269 billion messages every day. Email Security Challenge But… Continue reading.

Speaker: Erroll Amacker
Automation is transforming finance but without strong financial oversight it can introduce more risk than reward. From missed discrepancies to strained vendor relationships, accounts payable automation needs a human touch to deliver lasting value. This session is your playbook to get automation right. We’ll explore how to balance speed with control, boost decision-making through human-machine collaboration, and unlock ROI with fewer errors, stronger fraud prevention, and smoother operations.

Business Resilience Decoded
SEPTEMBER 19, 2018
Episode 4: "The Importance of Emotional Intelligence and Crisis Management" with Keith Frederick of Duke Clinical Research Institute at Duke University. Contact Frederick at [link] Episode 4: "The Importance of Emotional Intelligence and Crisis Management" with Keith Frederick of Duke Clinical Research Institute at Duke University.

Plan B Consulting
SEPTEMBER 14, 2018
Charlie looks at crisis communications and the steps you can take now to prepare your organisation for a potential cyber incident in the future. This week I am all cyber-ed up; on Monday and Tuesday I taught a great bunch of people attending our ‘Managing and Preparing for Cyber Incidents’ course, and on Wednesday morning I delivered a Cyber Briefing to a senior management team.

Crisis Response Journal
SEPTEMBER 17, 2018
Mohamed ELsonpaty, Adel Aldaghbashy, Zeki Al-Droubi, and Hazem Badr examine the link between conflict in disease, in an article originally written for the Science and Development Network (SciDev.Net).

Marketpoint Recall
SEPTEMBER 11, 2018
Peter Gillett is CEO of Zuant where he’s responsible for driving product development and client roll-outs of the company’s award-winning mobile lead capture app across US corporations. He is also CEO of Marketpoint Recall, a global recall and crisis management company. A pioneer in database marketing since the late 1970s, Peter is a serial entrepreneur.

Speaker: Tim Buteyn, President of ThinkingKap Learning Solutions
Join this brand new webinar with Tim Buteyn to learn how you can master the art of remote onboarding! By the end of this session, you'll understand how to: Craft a Tailored Onboarding Checklist 📝 Develop a comprehensive, customized checklist that ensures every new hire has a smooth transition into your company, no matter where they are in the world.

Alert Media
SEPTEMBER 12, 2018
The post Duty of Care Case Law And Your Business appeared first on AlertMedia.

Behavior Group
SEPTEMBER 14, 2018
Advocating for the return on investment (ROI) in IT security has traditionally been a challenge for IT professionals to communicate to management. IT teams are responsible for the complicated task of balancing budget limitations with strong protection that will reduce the risk of a cyberattack in today’s dynamic threat landscape. However, according to a recent… Continue reading.

Business Resilience Decoded
SEPTEMBER 19, 2018
Episode 4: "The Importance of Emotional Intelligence and Crisis Management" with Keith Frederick of Duke Clinical Research Institute at Duke University. Contact Frederick at [link] Episode 4: "The Importance of Emotional Intelligence and Crisis Management" with Keith Frederick of Duke Clinical Research Institute at Duke University. Contact Frederick at [link].

Plan B Consulting
SEPTEMBER 28, 2018
Charlie discusses the importance of quality over quantity when it comes to business continuity documents. This week I have been reviewing the level of emergency response, business continuity and crisis management of a utility in the Caribbean. As part of the review, I was asked to look at their security documents and procedures. I came across an inch-thick security manual, which I had to blow the dust off before looking at the contents inside.

Advertisement
Ensure your mid-year performance reviews are focused, productive, and growth-oriented with this practical checklist from Mitratech Trakstar. Designed for HR professionals, people managers, and team leads, this guide walks you through the full review process—from pre-meeting prep and feedback collection to action planning and follow-up. It also includes tips for creating a comfortable and effective review experience, plus ways to leverage tools like self-evaluations, PIPs, and development plans.

Crisis Response Journal
SEPTEMBER 16, 2018
Ali Moore, Vice Chancellor's Fellow at the University of Melbourne, examines whether Australia is prepared for the next health outbreak.

Marketpoint Recall
SEPTEMBER 14, 2018
In February 2018, the fast-food chicken chain KFC ran out of chicken. Because of a supply chain glitch, KFC was unable to get chicken to many of its United Kingdom restaurants. But it became more than a logistics problem when fans took to social media to voice their discontent, with some even reaching out to police via social media channels when the chain was forced to close many stores temporarily.

Alert Media
SEPTEMBER 6, 2018
The post How to Improve Lone Worker Safety appeared first on AlertMedia.

Behavior Group
SEPTEMBER 12, 2018
When it comes to cybersecurity, no doubt humans are the weakest link. No matter how many layers are added to your security stack, nor how much phishing education and awareness training you do, threat actors continue to develop more sophisticated ways to exploit the human vulnerabilities with socially engineered attacks. In fact, as security defenses… Continue reading.

Advertisement
Discover a clear, 5-step roadmap for business continuity plan testing. Whether you’re refining your existing business continuity plan or building one from scratch, understanding the right steps will make all the difference. Download the infographic to learn how to: Quickly identify and assess critical risks to your operations Conduct a focused Business Impact Analysis (BIA) to prioritize what matters most Develop a practical, action-ready business continuity plan tailored to your needs We’re her

Business Resilience Decoded
SEPTEMBER 14, 2018
Episode 3: "Racing With Blindspots" with Mike Mooney of Mooney Consulting Group. For more information, visit [link] - [link] - [link] Episode 3: "Racing With Blindspots" with Mike Mooney of Mooney Consulting Group.

Plan B Consulting
SEPTEMBER 28, 2018
Charlie discusses the importance of quality over quantity when it comes to business continuity documents. This week I have been reviewing the level of emergency response, business continuity and crisis management of a utility in the Caribbean. As part of the review, I was asked to look at their security documents and procedures. I came across an inch-thick security manual, which I had to blow the dust off before looking at the contents inside.

Crisis Response Journal
SEPTEMBER 5, 2018
A new study at Harvard has revealed a shocking statistic: CEOs spent just one per cent of their time working on crisis management.

Alert Media
SEPTEMBER 4, 2018
The post 5 Signs You Need to Upgrade Your Mass Notification System appeared first on AlertMedia.

Advertisement
Strengthen your operations with the Supply Chain Resilience Checklist. This practical, easy-to-use tool helps your organization prepare for disruptions and ensure long-term continuity in an unpredictable world. Why Download: Identify and assess critical supply chain risks Ask the right questions to evaluate vendor preparedness Implement effective strategies to reduce vulnerabilities Improve communication, transparency, and coordination across your network What You’ll Learn: How to evaluate and m

Business Resilience Decoded
SEPTEMBER 14, 2018
Episode 3: "Racing With Blindspots" with Mike Mooney of Mooney Consulting Group. For more information, visit [link] - [link] - [link] Episode 3: "Racing With Blindspots" with Mike Mooney of Mooney Consulting Group. For more information, visit [link] - [link] - [link].

Business Resilience Decoded
SEPTEMBER 4, 2018
Episode 1: "Developing a Successful Crisis Management Program" with Regina Phelps of Emergency Management & Safety Solutions. Website: [link] LinkedIn: [link] Episode 1: "Developing a Successful Crisis Management Program" with Regina Phelps of Emergency Management & Safety Solutions.

Business Resilience Decoded
SEPTEMBER 4, 2018
Episode 2: "America's Talent Pipeline – People Continuity" with Cheyene Marling of Firestorm People Solutions. Website: [link] LinkedIn: [link] Episode 2: "America's Talent Pipeline – People Continuity" with Cheyene Marling of Firestorm People Solutions.
Let's personalize your content