Creating a Multi-Region Application with AWS Services – Part 1, Compute and Security
AWS Disaster Recovery
DECEMBER 8, 2021
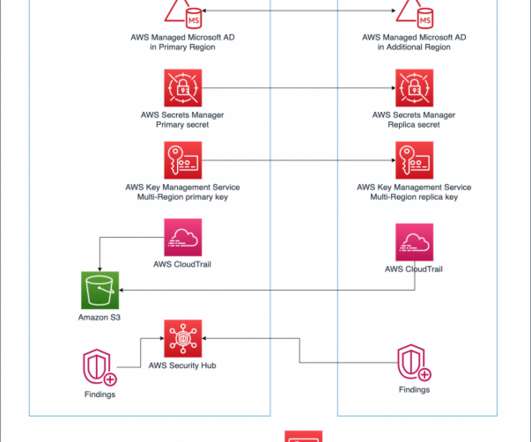
AWS Regions are built with multiple isolated and physically separate Availability Zones (AZs). This approach allows you to create highly available Well-Architected workloads that span AZs to achieve greater fault tolerance. Considerations before getting started. Ensuring security, identity, and compliance.

















Let's personalize your content