Governance 101: Why Separation of Duties is Non-Negotiable
LogisManager
MARCH 14, 2025
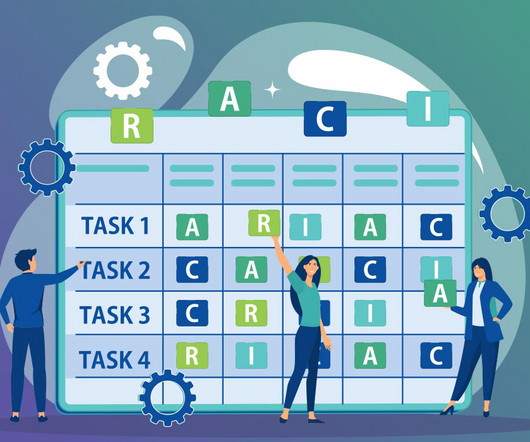
It ensures that no single person can execute all parts of a transaction or process , preventing unchecked authority, reducing risk, and strengthening oversight. Risk Assessment: Those evaluating risks shouldnt be responsible for mitigating them. Risk Owner Takes responsibility for risk mitigation.













































Let's personalize your content