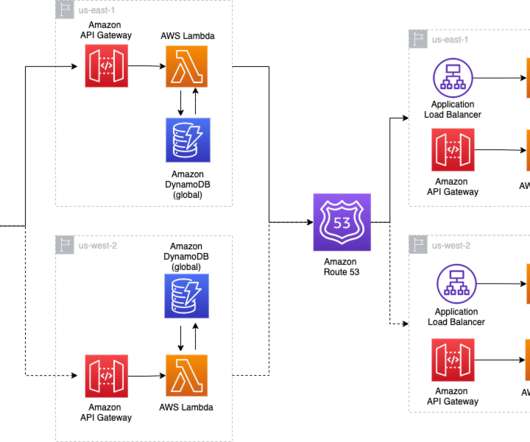
Implementing Multi-Region Disaster Recovery Using Event-Driven Architecture
AWS Disaster Recovery
JULY 27, 2021
In this blog post, we share a reference architecture that uses a multi-Region active/passive strategy to implement a hot standby strategy for disaster recovery (DR). This makes your infrastructure more resilient and highly available and allows business continuity with minimal impact on production workloads. Testing and results.












Let's personalize your content