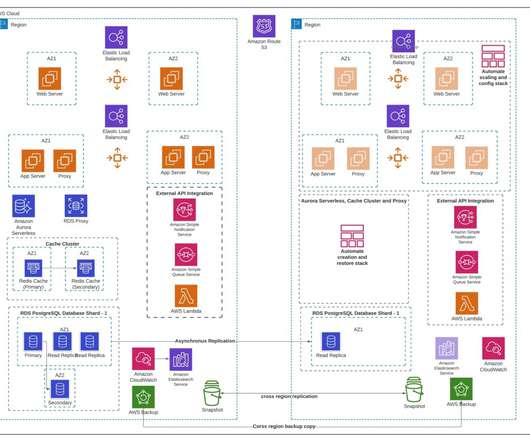
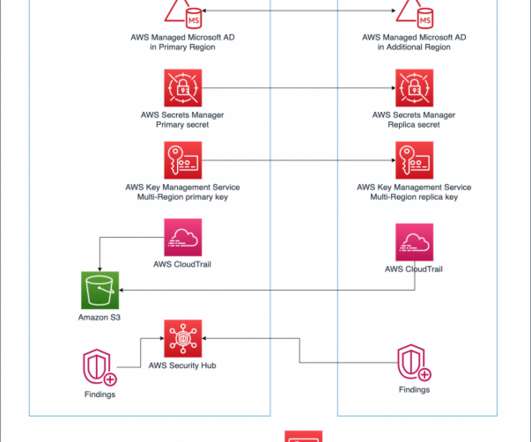
Top Architecture Blog Posts of 2023
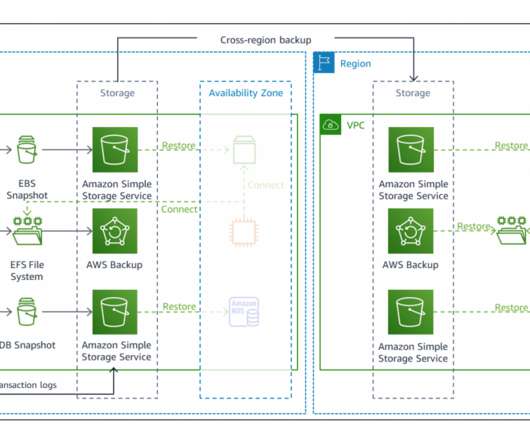
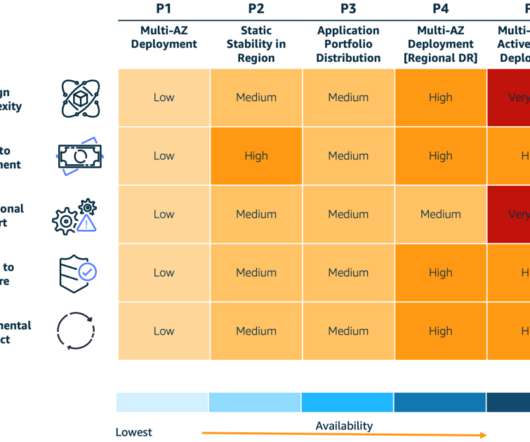
AWS Disaster Recovery
FEBRUARY 28, 2024
2023 was a rollercoaster year in tech, and we at the AWS Architecture Blog feel so fortunate to have shared in the excitement. As always, thanks to our readers and to the many talented and hardworking Solutions Architects and other contributors to our blog. Building endless aisle architecture for order processing Check it out!











































Let's personalize your content