Understand resiliency patterns and trade-offs to architect efficiently in the cloud
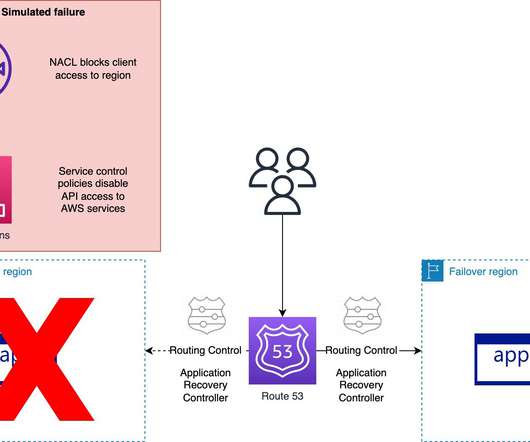
AWS Disaster Recovery
JUNE 3, 2022
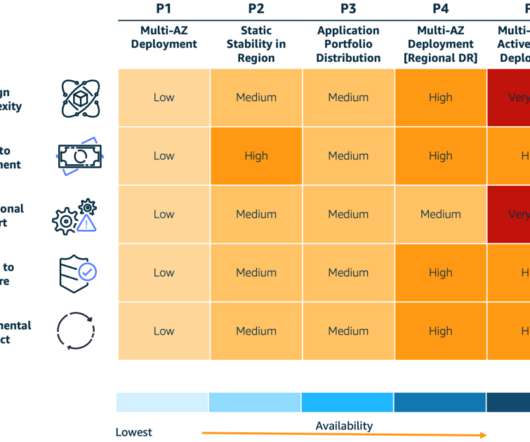
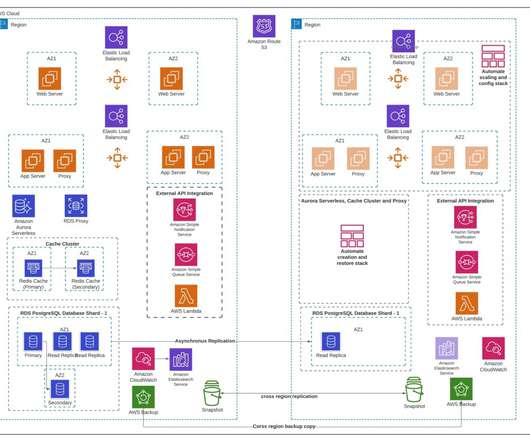
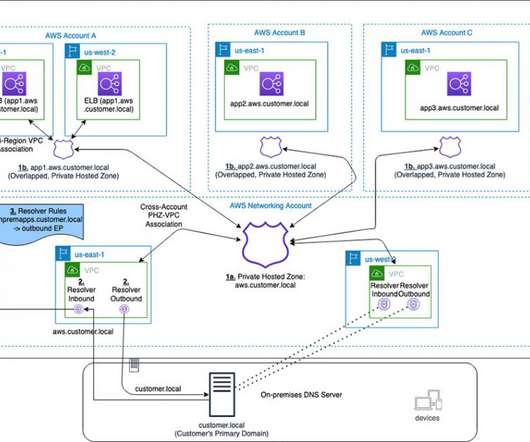
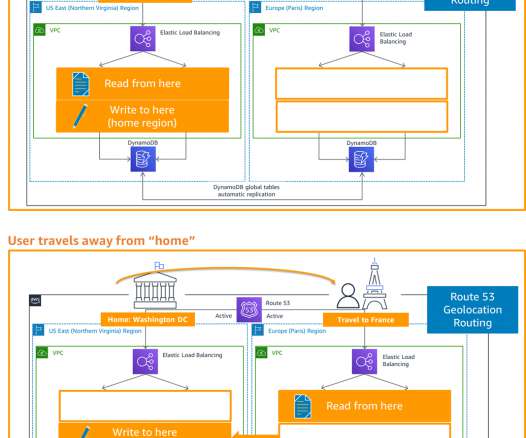
Example Corp has multiple applications with varying criticality, and each of their applications have different needs in terms of resiliency, complexity, and cost. The P1 pattern uses a Multi-AZ architecture where applications operate in multiple AZs within a single AWS Region. P3 – Application portfolio distribution.
















Let's personalize your content