Case Study: Transforming LogicManager
LogisManager
OCTOBER 15, 2024
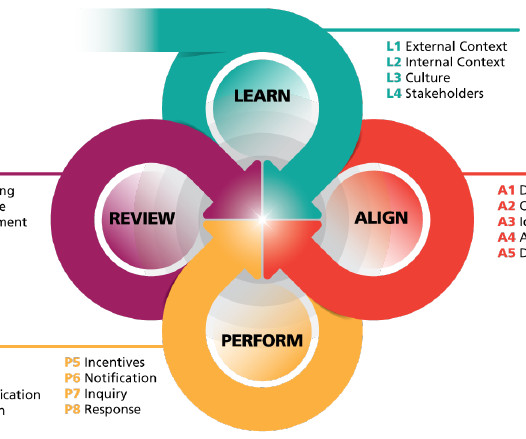
For instance, when a metric deviated from the norm, we drilled down to discover that coordination of activities had become more challenging with remote work. With this visibility into performance trends, we can target specific areas for improvement, aligning resources where they have the most impact.











































Let's personalize your content