Bringing Data Analytics into the Hardware Design Story
Pure Storage
SEPTEMBER 14, 2023
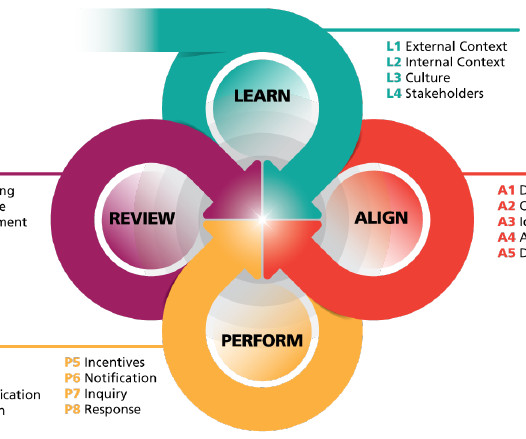
An array may physically be on a data center floor, but we’re still actively monitoring it back here at Pure. Additional dashboards monitoring our internal systems helped us evaluate our initial hypothesis—that there was a dependence on temperature—while we performed controlled testing.


















Let's personalize your content