What is COBIT? COBIT Explained
BMC
DECEMBER 5, 2024
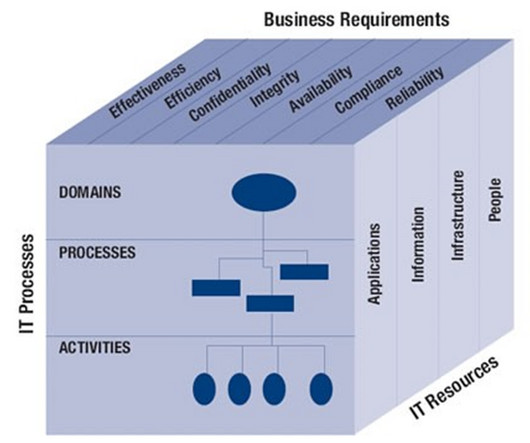
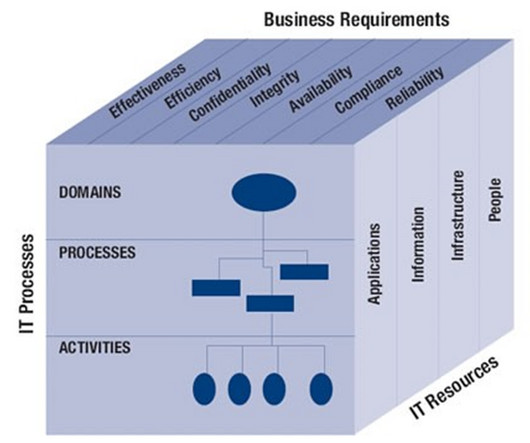
Its latest iteration, COBIT 2019 , has revamped parts of its framework while offering much-needed updates that accounts for ever-present cybersecurity threats and the incorporation of Agile and DevOps practices. ISACA stands for the Information Systems Audit and Control Association. What is ISACA? What are the benefits of COBIT?















Let's personalize your content