Hazardous Conditions: Mitigation Planning and Pandemics
National Center for Disaster Prepardness
MAY 12, 2021
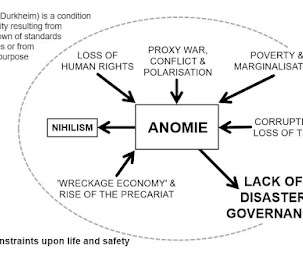
state develops a hazard mitigation plan, which identifies top local risks and provides a framework for long term strategies to reduce risk and protect citizens and property from damage. 8 states/territories mention pandemic planning but do not discuss further how the state or agency will be able to mitigate the hazard from the event.














Let's personalize your content