Double trouble: When climate change and cyber crime collide
everbridge
NOVEMBER 11, 2024
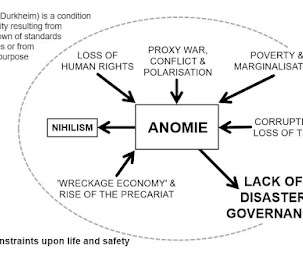
During disasters, distracted, weakened, and vulnerable businesses and individuals are easy targets for cyber criminals. Additionally, the vulnerability of critical infrastructure like power grids, communication networks, and transportation systems during times of crisis makes them prime targets for state-sponsored cyberattacks.














Let's personalize your content